Please click here to view our CyberSecurity Assessment Services.
The Threat to Computer Systems
Cybersecurity threats are the second highest source of risk according to the Gartner Board of Directors Survey; regulatory compliance is number one. Boards are asking for more visibility into how their organizations are protecting their information systems because of the constant assault of hackers. The Kaspersky global real time threat mapping shows this new reality as millions of attacks are launched every second of each day.
As a result of this risk, Gartner expects a dramatic increase in Boards having a dedicated cybersecurity committee in the near future. Destiny Corporation is ready to assist with its proven Four-Step Threat Solution plan. The plan uses the latest technology and cyber techniques to help prevent, detect, and remediate threats. The dangers are both external and internal, from the complex (such as network) to the simple and cheapest (which are passwords).
Passwords are one of the most vulnerable areas of an organization. They account for nearly half of all cyberattacks according to a recent Gartner study. Imagine reducing your risk by 50% which should greatly please the Board. Destiny Corporation can help.
The Problem with Passwords
The largest vulnerability in information security is from humans, not technology. Nearly 8 in 10 cybercrimes start with a simple password hack. Here are facts on why passwords pose a significant risk.
-
- 81% of hacking-related breaches were caused by password compromise.
- 65% of people reuse passwords across multiple, if not all, sites.
- 14 times is the average reuse of passwords by each individual.
- 73% of users duplicate their passwords in both their personal and work accounts.
- 91% of respondents claim to understand the risks of reusing passwords across multiple accounts, but 59% admitted to doing it anyway.
- 44 million accounts were vulnerable to account takeover due to compromised or stolen passwords.
The biggest difficulty with passwords is there are too many to track in these digital times. The average person has over 100 accounts with passwords to maintain. As a result, people are remiss when managing their passwords. This lack of care creates an opening for bad actors as shown above. This is why we include password protection as a foundation of our 4 step Cyber Prevention Solution.
Password Solution to Remove 80% of Cyber Threats
There are several ways to enhance your password protection.
- Change it every 60 days.
- Establish a length of at least eight characters.
- Use both upper- and lower-case characters.
- Include a combination of alphanumeric characters and symbols.
- Make it unique (for only one profile/website).
- Store it using a reversible encryption.
Doing each one of these is extremely difficult to enforce. Our solution creates a strong encrypted random password containing a combination of alphanumeric characters and symbols. Destiny makes password protection – Easy to use – Easy to implement – Easy to protect.
Contact us to learn how to alleviate Cyber Threats with Secure Password Management.
Destiny's Four Step Cyber Prevention Solution
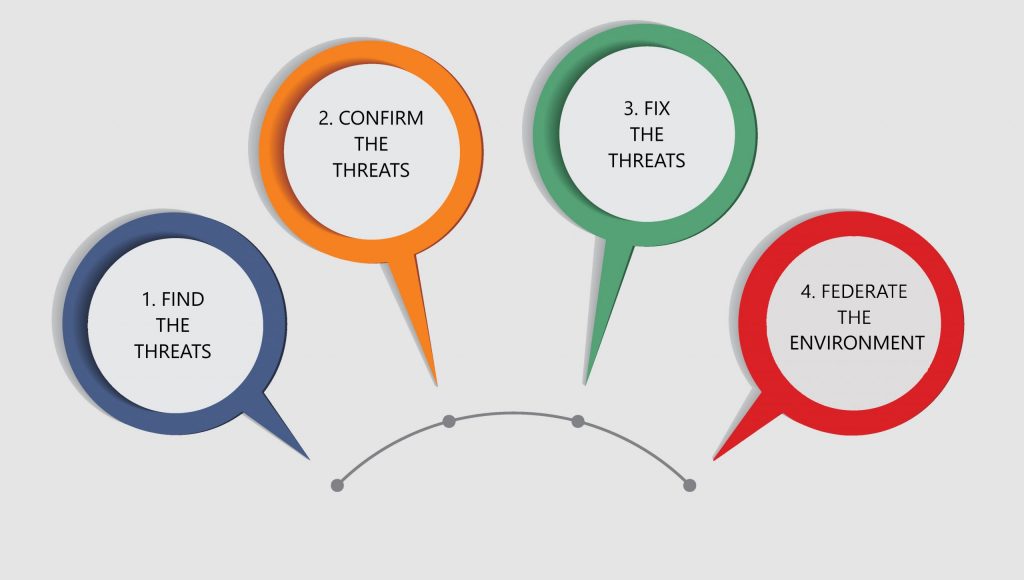
Find the Threats
Logs track the activity of the computer but can be altered by hackers to say anything and can be difficult to locate evidence then. If logs were the only tool that required investigation the ransomware could be detected with its examination.
Flows are the more likely place to see evidence of the problems – conversation between computers – and they cannot be easily modified and totally avoid detection. The router or switch monitors this dialog and a File Hash can be found.
In government systems, Forensics can be used, since the person’s actions are recorded and can be played back to show what the person did exactly.
User Behavior Analytics is the combination of Logs and Flows, and how the two relate to each other, and it varies from one user to another. As a result, a deviation from normal behavior for a specific person can be noticed by the software.
Half of the threats identified are caused by internal users as opposed to external threats from outside the organization.
Confirm the Threats
Did an assumed adverse action occur? Known threats are often Googled by investigators but only 20% are listed — so additional confirmation approaches are needed. A threat intelligence organization can provide details on these menaces or AI can be used instead.
Confirmation may take an expert 6 to 8 hours of investigation, or it can be done in about five minutes with AI.
False positives are mislabeled security alerts and the threat is indicated when there is none. They may be caused by software bugs, software that is written badly, or even unrecognized network traffic.
The majority of security staff are used to ignoring false positives, but this can cause them to miss actual threats. This occurred in the Target data breach. Nevertheless, investigation of false alerts is often a large waste of time.
Regular testing of security software is the way to minimize prior known threats in addition to current unknown cybersecurity risks. In addition, whitelisting (or default-deny of unauthorized software) has proven effective – even on morphing software that changes itself.
Fix the Threats
The worst situation is Zero Day Attacks because they are a complete unknown – no data has been collected on them this early. But if, for example, brand new servers are brought online with the addition of malware then organizations rely on expert teams that can quickly block the malware to protect systems.
Awareness and automation together is how protection is maintained. And awareness can only occur with experience.
Federate the Environment
Finally, consider the industry of the organization, and have queries run that typify the current threats to that type of firm to see if the result shows a specific type of malware. This is utilization of security intelligence and the most proactive investigation.
If a variety of known components are examined by security analytics (Intrusion Prevention System, firewall, IDs) then ongoing system examination can find discrepancies very quickly.
The key to this step is that the data being queried does not have to be moved. This streamlines the analytics process.
Destiny CyberSecurity Assessment Service Offerings
Free Assessments (one of two options)
- Directory/Server/Network Threat Assessment
- Perimeter Security Assessment
CyberSecurity Assessments
- Endpoint and Mobile Device Assessment – Evaluate current implementations for managing endpoints and devices.
- Governance, Risk and Compliance:
- Policies and Procedures Assessment – Ensures documented IT policies and procedures are aligned with best practices and regulatory requirements.
- Security Risk Assessment – Top-down analysis of an organization’s security preparedness.
- Business and Technical Security Strategy Development – Provide customers with tactical and strategic planning that aligns with business and technical requirements.
- Security Incident and Response Planning – Protects data assets throughout the incident response process including secure backups, leveraging logs, and security alerts to detect malicious activity.
- Business Continuity / Disaster Recovery and Backup Planning:
- Current state appraisal
- Business impact analysis
- Threat and risk assessment
- IT Assessments and Strategy/Solutions Development – People, process, and technology relationship with emphasis on Technology platforms and operations.
Ransomware
There are different forms of ransomware attacks with variations in damage capability. The average cost to an organization that is victimized by ransomware exceeds $1 million. The average down time is 9.6 days.
In addition, the CEO is often fired while the brand value declines. Although insurance may cover the loss, premiums will rise significantly.
The Major Types of Ransomware.
Crypto malware. This encrypts files, folders, and hard drives and it has spread within global corporate networks.
Lockers. Devices cannot be accessed because users are locked out. It is often based in Android.
Scareware. Scareware acts like an antivirus or “cleaning” instrument. The explanation usually indicates that there are problems with the computer and requesting money to fix the trouble. It may lock the computer or place alerts or pop-up messages on the screen.
Doxware. Alternate names are leakware or extortionware. It contains a threat to publish stolen information online if ransom is not paid.
RaaS. This malware is also known as “Ransomware as a service”. It is hosted anonymously and includes malware distribution, payment collection, and decryptor management. Operators get a portion of the ransom to support the nefarious business.
Mobile ransomware. A malicious application indicates a device lock due to illegal activity.
WhiteRose. A recent type of distinctive ransomware attacks with unusual ransom notes. Its payload may be delivered through unsecured Remote Desktop services, though the exact method has not been determined.
Whiteware. A virus enters your systems and deletes every file.
Case Studies
Two harmful ransomware examples are described below.
In March, 2018 a ransomware virus attacked Atlanta government computer systems by guessing weak passwords. Two months earlier, an audit found over 1500 vulnerabilities in the city’s systems. In June, 2018 about one third of the Atlanta software systems were offline or disabled, and many files were permanently deleted.
Contractors were allocated $2.7 million to recover, but later estimated the total cost at $9.5 million. More details are available at the following link.
In 2019, a credit monitoring firm found that 37,000 people had data compromised after a legitimate password was used to break into their systems. The access had occurred about a month earlier. The firm stated it was not a breach, but clearly this indicates poor systems design. For more information click the link below.

